The smart Trick of Risk Management Enterprise That Nobody is Talking About
Table of ContentsLittle Known Facts About Risk Management Enterprise.Top Guidelines Of Risk Management EnterpriseThe Basic Principles Of Risk Management Enterprise The Best Strategy To Use For Risk Management EnterpriseHow Risk Management Enterprise can Save You Time, Stress, and Money.Not known Details About Risk Management Enterprise Unknown Facts About Risk Management Enterprise
Real-Time Risk Analyses and Mitigation in this software application permit organizations to continuously monitor and assess dangers as they evolve. Once dangers are identified, the software application assists in immediate mitigation activities.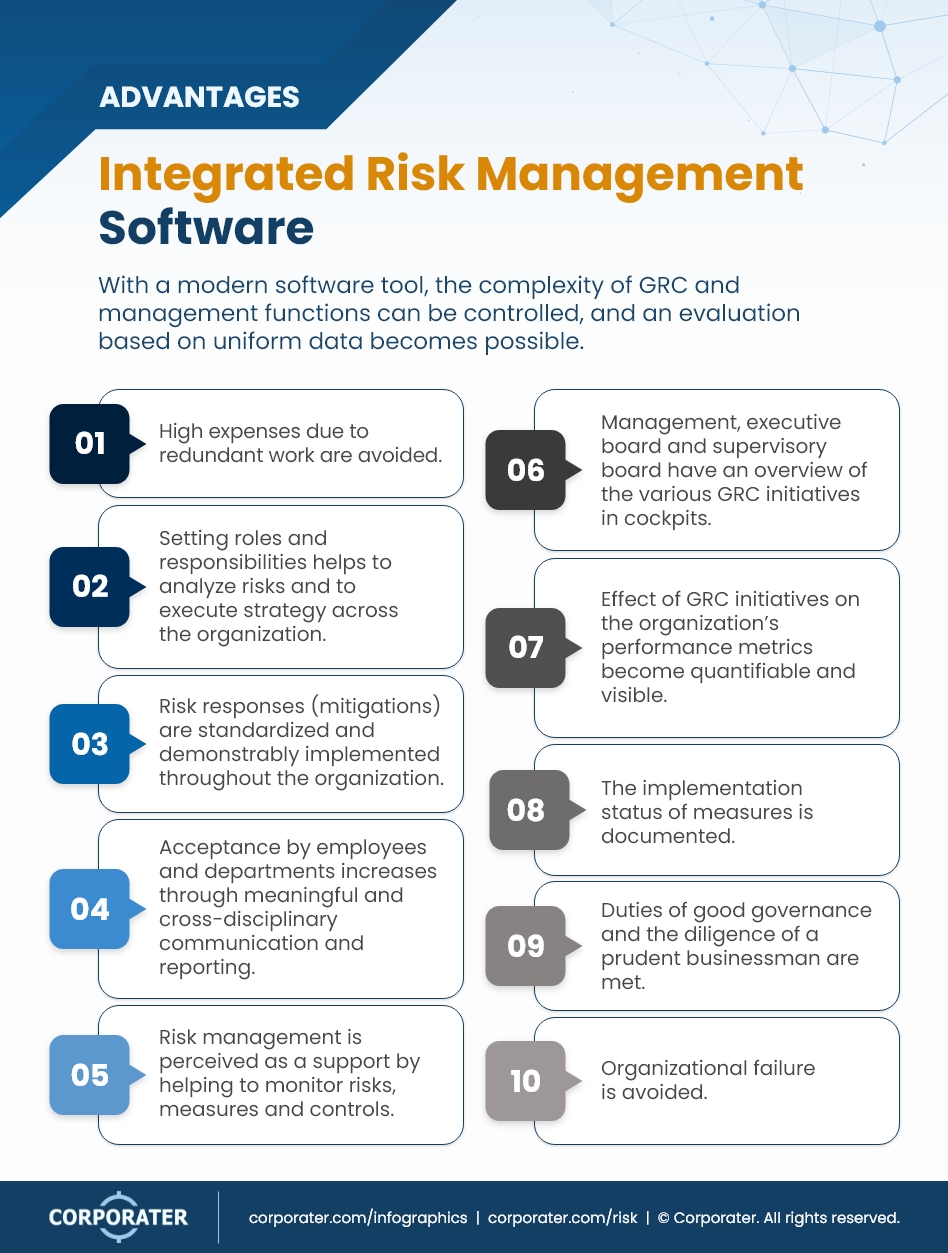
They resolve the challenge of ongoing risk monitoring by offering tools to check dangers continually. KRIs boost security threat oversight, guaranteeing that prospective risks are recognized and handled efficiently.
The 10-Minute Rule for Risk Management Enterprise
IT risk monitoring is a part of business threat administration (ERM), developed to bring IT run the risk of according to an organization's danger hunger. IT risk monitoring (ITRM) includes the policies, treatments and innovation essential to lower risks and vulnerabilities, while maintaining compliance with appropriate regulatory needs. Additionally, ITRM looks for to limit the consequences of damaging occasions, such as security violations.
Veronica Rose, ISACA board supervisor and a details systems auditor at Metropol Corp. The ISACA Threat IT framework straightens well with the COBIT 2019 framework, Rose claimed.
Venture Risk Management Software Application Development: Perks & Qualities, Expense. With technical advancements, risks are constantly on the surge. That being claimed, companies are most likely to deal with challenges that affect their finances, operations, and track record. From swiftly changing markets to regulative adjustments and cyber hazards, companies navigate via a regularly altering sea of risks.
Get This Report on Risk Management Enterprise
In this blog site, we will dive right into the world of ERM software application, discovering what it is, its advantages, features, and so on so that you can construct one for your company. Venture Danger Monitoring (ERM) software application is the application program for planning, guiding, arranging, and regulating service tasks and streamlining threat monitoring procedures.
With ERM, organizations can make informative choices to boost the overall strength of business. Read: ERP Application Development Devoted ERM systems are essential for companies that regularly handle huge quantities of delicate info and multiple stakeholders to accept strategic decisions. Some sectors where ERM has actually become a conventional system are healthcare, finance, building and construction, insurance, and infotech (IT).
: It is difficult for any kind of enterprise to go through an extensive audit. It can be stayed clear of by making use of the ERM software program system. This system automates law conformity monitoring to maintain the organization safe and certified. Aside from that, it also logs and categorizes all the data in the system making it less complicated for auditors to review procedures a lot faster.
All About Risk Management Enterprise
You can likewise attach existing software program systems to the ERM via APIs or by including information by hand. Businesses can make use of ERM to examine risks based on their potential impact for much better danger administration and mitigation.: Including this attribute enables individuals to obtain real-time notifications on their devices about any risk that could take place and its impact.
Instead, the software permits them to establish limits for different procedures and send press alerts in case of feasible threats.: By integrating information visualization and reporting in the custom ERM software application, services can gain clear understandings about threat fads and performance.: It is obligatory for companies to follow sector conformity and regulatory criteria.

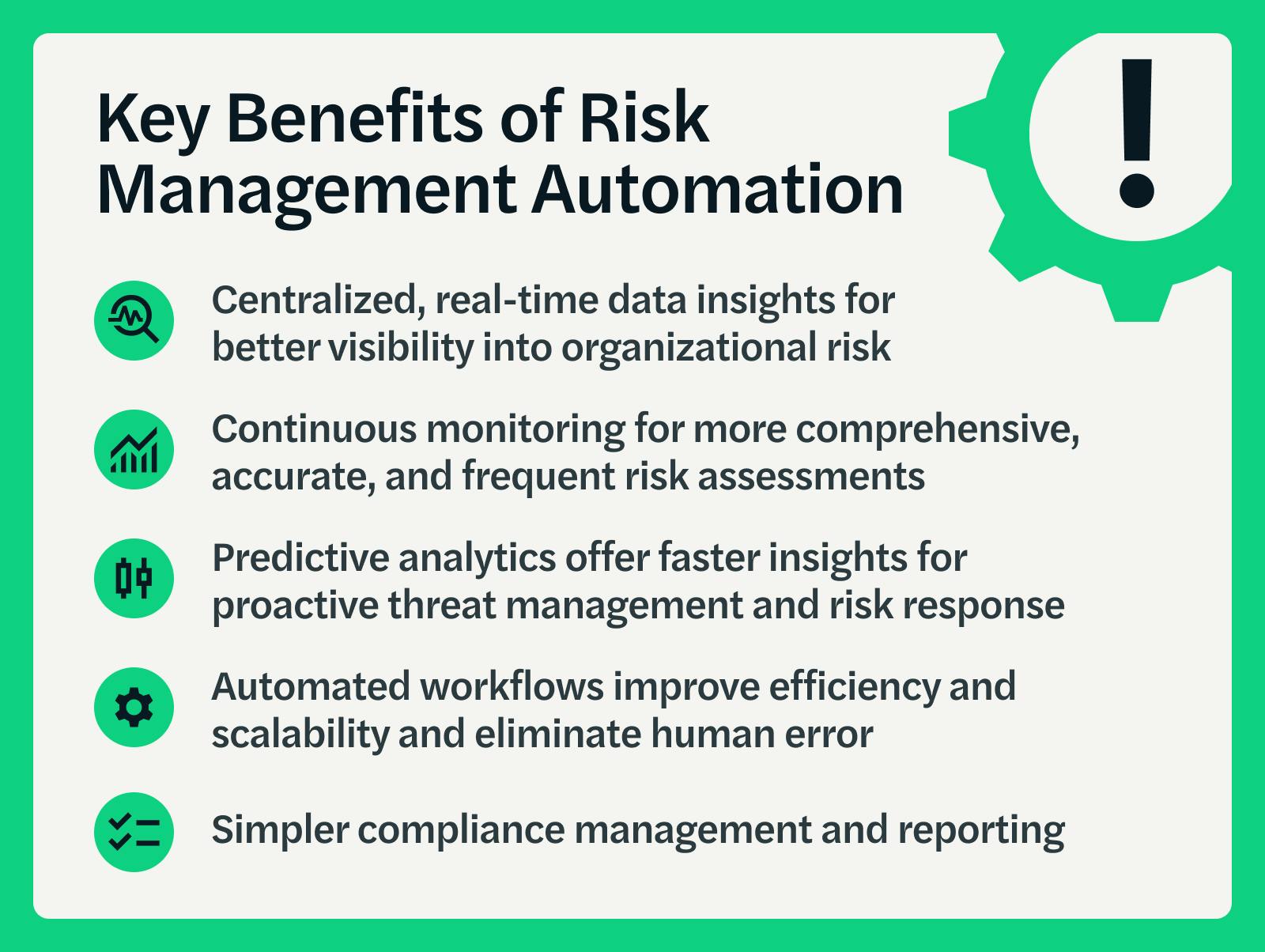
These platforms enable firms to apply best-practice danger management processes that line up with industry standards, offering an effective, technology-driven strategy to recognizing, evaluating, and mitigating threats. This blog site discovers the benefits of computerized threat administration devices, the areas of danger management they can automate, and the worth they give an organization.
Risk Management Enterprise Fundamentals Explained
Groups can establish forms with the appropriate fields and quickly produce various kinds for different danger types. These danger evaluation types can be distributed for conclusion via automated operations that send notifications to the appropriate personnel to complete the types online. If kinds are not completed by navigate to this site the target date, then chaser e-mails are automatically sent by the system.
The control monitoring and control testing procedure can likewise be automated. Firms can utilize computerized operations to send out routine control test alerts and personnel can go into the results using on the internet forms. Controls can also be kept an eye on by the software by establishing policies to send out notifies based upon control data kept in various other systems and spread sheets that is pulled right into the system by means of API combinations.
Danger administration automation software program can additionally support with threat reporting for all degrees of the enterprise. Leaders can check out records on risk direct exposure and control effectiveness via a range of reporting results including static reports, Power BI interactive records, bowtie evaluation, and Monte Carlo simulations. The capacity to pull actual time reports at the touch of a switch eliminates arduous data manipulation tasks leaving danger teams with even more time to assess the data and encourage business on the ideal strategy.
Organizations operating in competitive, fast-changing markets can't manage hold-ups or inadequacies in resolving prospective threats. Traditional threat management using manual spreadsheet-based processes, while acquainted, typically lead to fragmented data, time-consuming reporting, and an increased possibility of human mistake.
The Greatest Guide To Risk Management Enterprise
This ensures risk signs up are constantly current and aligned with business objectives. Conformity is an additional crucial chauffeur for automating danger management. Criteria like ISO 31000, CPS 230 and COSO all give support around danger administration finest techniques and control frameworks, and automated risk management tools are structured to align with these needs helping companies to satisfy most typically made use of threat management standards.
Try to find danger software systems with a consents pecking order to conveniently establish operations for danger escalation. This capability enables you to customize the view for each customer, so they only see the information pertinent to them. Ensure the ERM software uses customer monitoring so you can see that entered what information and when.
Seek out devices that use task danger monitoring abilities to manage your tasks and portfolios and the linked risks. The advantages of adopting risk monitoring automation software prolong much beyond performance.

Some Known Facts About Risk Management Enterprise.
While the situation for automation is engaging, implementing a risk monitoring platform is not without its obstacles. For one, data quality is crucial. Automated systems count on exact, updated details to provide meaningful insights. To get over the challenges of threat management automation, companies have to buy data cleaning and governance to guarantee a solid structure for applying an automated system.
Automation in risk monitoring empowers businesses to change their method to take the chance of and construct a more powerful foundation for the future (Risk Management Enterprise). The concern is no more whether to automate threat monitoring, it's just how quickly you can start. To see the Riskonnect at work,
The response typically exists in how well risks are prepared for and managed. Task administration software works as the navigator in the tumultuous waters of job execution, offering tools that determine and examine threats and devise strategies to mitigate them properly. From real-time information analytics to comprehensive risk monitoring dashboards, these tools supply a 360-degree view of the This Site project landscape, making it possible for task managers to make educated choices that maintain their tasks on track and within spending plan.